-
John the Ripper: A Guide to Password Cracking Techniques
John the Ripper was initially developed to detect weak Unix passwords, but over time, it has expanded to support a wide range of operating systems and hashing algorithms. This tool can now handle various encrypted password formats, such as Unix/Linux, Windows, and even database-specific hashes. John can also tackle different types of encryption, including DES,… Read more
-
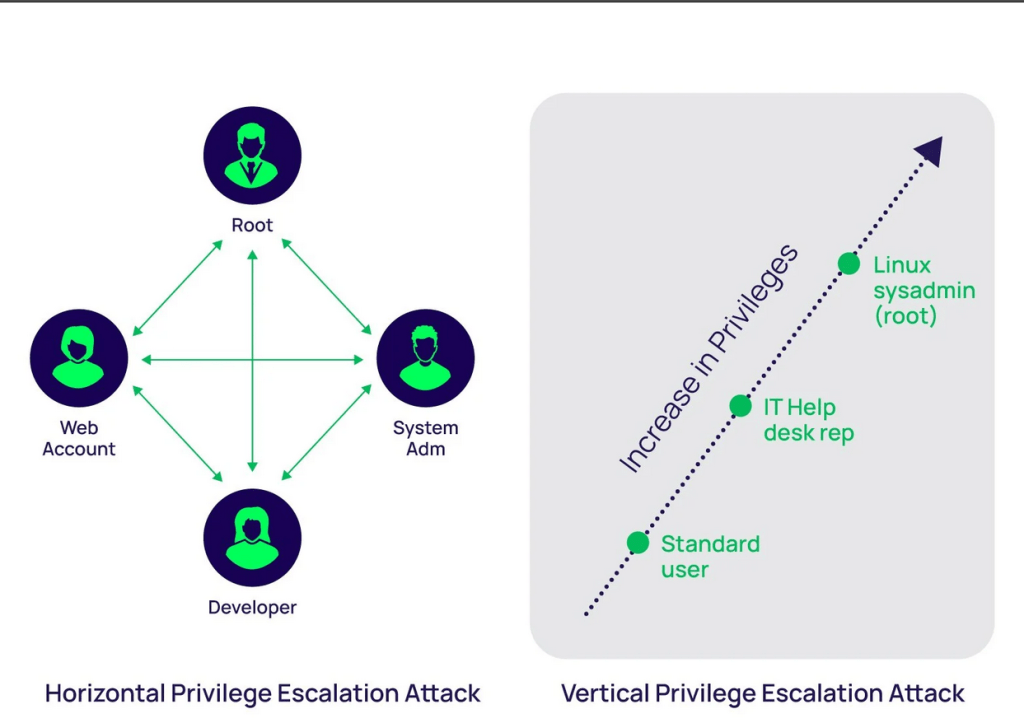
Common Methods of Linux Privilege Escalation
Privilege Escalation fundamentally refers to moving from lower to higher permissions. More specifically, it involves exploiting a vulnerability, design flaw, or configuration error in an operating system or application to gain unauthorized access to resources that are typically restricted from the user. Read more
-
Maximizing Security with OpenVPN: Use Cases and Set-Up Guide
OpenVPN is a highly popular and versatile open-source software that enables secure point-to-point or site-to-site connections using virtual private network (VPN) techniques. Since its introduction in 2001, OpenVPN has become one of the most trusted solutions for establishing encrypted communications over the internet, providing users with robust security and privacy. Read more
-
SSH: Secure Remote Login and Data Encryption
SSH was born out of necessity in 1995, thanks to Finnish computer scientist Tatu Ylönen. He saw the risks in sending data over the internet using plaintext protocols like Telnet, which is akin to shouting your secrets in a crowded room. So, he developed SSH to provide a secure channel over an insecure network in… Read more
-
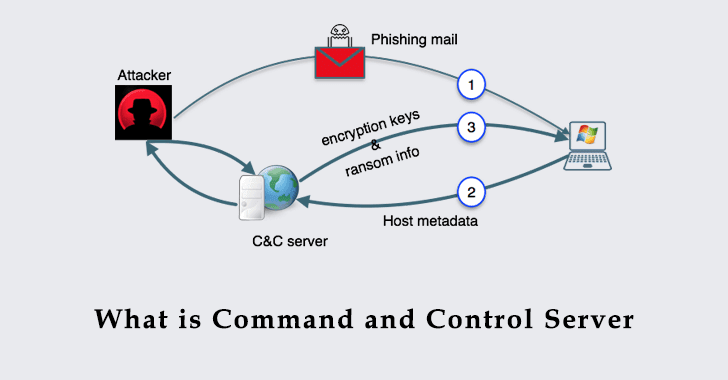
Unveiling the Significance of Command and Control (C2) Servers in Cybersecurity
In the vast and intricate web of cybersecurity, Command and Control (C2) servers emerge as pivotal players in the digital shadows. These servers, often shrouded in mystery, are the masterminds behind the strings of cyberattacks that we hear about in the news. But what exactly are these C2 servers, and why are they so crucial… Read more
-

Air-Gapped Computers: Safeguarding Sensitive Information and Preventing Cyber Threats
Imagine you have a top-secret recipe for the best chocolate cake in the world, and you want to make sure no one can steal it. You decide to write it down and lock it in a safe that’s completely isolated from the outside world. This is the idea behind an air-gapped computer. It’s a computer… Read more
Designed with WordPress